- Introduction
-
Getting Started
- Creating an Account in Hevo
- Subscribing to Hevo via AWS Marketplace
- Subscribing to Hevo via Snowflake Marketplace
- Connection Options
- Familiarizing with the UI
- Creating your First Pipeline
- Data Loss Prevention and Recovery
-
Data Ingestion
- Types of Data Synchronization
- Ingestion Modes and Query Modes for Database Sources
- Ingestion and Loading Frequency
- Data Ingestion Statuses
- Deferred Data Ingestion
- Handling of Primary Keys
- Handling of Updates
- Handling of Deletes
- Hevo-generated Metadata
- Best Practices to Avoid Reaching Source API Rate Limits
-
Edge
- Getting Started
- Data Ingestion
- Core Concepts
-
Pipelines
- Familiarizing with the Pipelines UI (Edge)
- Creating an Edge Pipeline
- Working with Edge Pipelines
- Object and Schema Management
- Pipeline Job History
-
Sources
- PostgreSQL
- Oracle
- MySQL
- SQL Server
- Troubleshooting Database Sources
- Salesforce Bulk API V2
- Ordergroove
- BambooHR
- Stripe
- NetSuite SuiteAnalytics
- Shopify
- Naming Conventions for Source Data Entities
- Destinations
- Alerts
- Custom Connectors
-
Releases
- Edge Release Notes - April 20, 2026
- Edge Release Notes - April 09, 2026
- Edge Release Notes - March 31, 2026
- Edge Release Notes - March 26, 2026
- Edge Release Notes - March 16, 2026
- Edge Release Notes - February 18, 2026
- Edge Release Notes - February 10, 2026
- Edge Release Notes - February 03, 2026
- Edge Release Notes - January 20, 2026
- Edge Release Notes - December 08, 2025
- Edge Release Notes - December 01, 2025
- Edge Release Notes - November 05, 2025
- Edge Release Notes - October 30, 2025
- Edge Release Notes - September 22, 2025
- Edge Release Notes - August 11, 2025
- Edge Release Notes - July 09, 2025
- Edge Release Notes - November 21, 2024
-
Data Loading
- Loading Data in a Database Destination
- Loading Data to a Data Warehouse
- Optimizing Data Loading for a Destination Warehouse
- Deduplicating Data in a Data Warehouse Destination
- Manually Triggering the Loading of Events
- Scheduling Data Load for a Destination
- Loading Events in Batches
- Data Loading Statuses
- Data Spike Alerts
- Name Sanitization
- Table and Column Name Compression
- Parsing Nested JSON Fields in Events
-
Pipelines
- Data Flow in a Pipeline
- Familiarizing with the Pipelines UI
- Working with Pipelines
- Managing Objects in Pipelines
- Pipeline Jobs
-
Transformations
-
Python Code-Based Transformations
- Supported Python Modules and Functions
-
Transformation Methods in the Event Class
- Create an Event
- Retrieve the Event Name
- Rename an Event
- Retrieve the Properties of an Event
- Modify the Properties for an Event
- Fetch the Primary Keys of an Event
- Modify the Primary Keys of an Event
- Fetch the Data Type of a Field
- Check if the Field is a String
- Check if the Field is a Number
- Check if the Field is Boolean
- Check if the Field is a Date
- Check if the Field is a Time Value
- Check if the Field is a Timestamp
-
TimeUtils
- Convert Date String to Required Format
- Convert Date to Required Format
- Convert Datetime String to Required Format
- Convert Epoch Time to a Date
- Convert Epoch Time to a Datetime
- Convert Epoch to Required Format
- Convert Epoch to a Time
- Get Time Difference
- Parse Date String to Date
- Parse Date String to Datetime Format
- Parse Date String to Time
- Utils
- Examples of Python Code-based Transformations
-
Drag and Drop Transformations
- Special Keywords
-
Transformation Blocks and Properties
- Add a Field
- Change Datetime Field Values
- Change Field Values
- Drop Events
- Drop Fields
- Find & Replace
- Flatten JSON
- Format Date to String
- Format Number to String
- Hash Fields
- If-Else
- Mask Fields
- Modify Text Casing
- Parse Date from String
- Parse JSON from String
- Parse Number from String
- Rename Events
- Rename Fields
- Round-off Decimal Fields
- Split Fields
- Examples of Drag and Drop Transformations
- Effect of Transformations on the Destination Table Structure
- Transformation Reference
- Transformation FAQs
-
Python Code-Based Transformations
-
Schema Mapper
- Using Schema Mapper
- Mapping Statuses
- Auto Mapping Event Types
- Manually Mapping Event Types
- Modifying Schema Mapping for Event Types
- Schema Mapper Actions
- Fixing Unmapped Fields
- Resolving Incompatible Schema Mappings
- Resizing String Columns in the Destination
- Changing the Data Type of a Destination Table Column
- Schema Mapper Compatibility Table
- Limits on the Number of Destination Columns
- File Log
- Troubleshooting Failed Events in a Pipeline
- Mismatch in Events Count in Source and Destination
- Audit Tables
- Activity Log
-
Pipeline FAQs
- Can multiple Sources connect to one Destination?
- What happens if I re-create a deleted Pipeline?
- Why is there a delay in my Pipeline?
- Can I change the Destination post-Pipeline creation?
- Why is my billable Events high with Delta Timestamp mode?
- Can I drop multiple Destination tables in a Pipeline at once?
- How does Run Now affect scheduled ingestion frequency?
- Will pausing some objects increase the ingestion speed?
- Can I see the historical load progress?
- Why is my Historical Load Progress still at 0%?
- Why is historical data not getting ingested?
- How do I set a field as a primary key?
- How do I ensure that records are loaded only once?
- Why can't I see my Pipelines after logging in?
- Events Usage
-
Sources
- Free Sources
-
Databases and File Systems
- Data Warehouses
-
Databases
- Connecting to a Local Database
- Amazon DocumentDB
- Amazon DynamoDB
- Elasticsearch
-
MongoDB
- Generic MongoDB
- MongoDB Atlas
- Support for Multiple Data Types for the _id Field
- Example - Merge Collections Feature
-
Troubleshooting MongoDB
-
Errors During Pipeline Creation
- Error 1001 - Incorrect credentials
- Error 1005 - Connection timeout
- Error 1006 - Invalid database hostname
- Error 1007 - SSH connection failed
- Error 1008 - Database unreachable
- Error 1011 - Insufficient access
- Error 1028 - Primary/Master host needed for OpLog
- Error 1029 - Version not supported for Change Streams
- SSL 1009 - SSL Connection Failure
- Troubleshooting MongoDB Change Streams Connection
- Troubleshooting MongoDB OpLog Connection
-
Errors During Pipeline Creation
- SQL Server
-
MySQL
- Amazon Aurora MySQL
- Amazon RDS MySQL
- Azure MySQL
- Generic MySQL
- Google Cloud MySQL
- MariaDB MySQL
-
Troubleshooting MySQL
-
Errors During Pipeline Creation
- Error 1003 - Connection to host failed
- Error 1006 - Connection to host failed
- Error 1007 - SSH connection failed
- Error 1011 - Access denied
- Error 1012 - Replication access denied
- Error 1017 - Connection to host failed
- Error 1026 - Failed to connect to database
- Error 1027 - Unsupported BinLog format
- Failed to determine binlog filename/position
- Schema 'xyz' is not tracked via bin logs
- Errors Post-Pipeline Creation
-
Errors During Pipeline Creation
- MySQL FAQs
- Oracle
-
PostgreSQL
- Amazon Aurora PostgreSQL
- Amazon RDS PostgreSQL
- Azure PostgreSQL
- Generic PostgreSQL
- Google Cloud PostgreSQL
- Heroku PostgreSQL
-
Troubleshooting PostgreSQL
-
Errors during Pipeline creation
- Error 1003 - Authentication failure
- Error 1006 - Connection settings errors
- Error 1011 - Access role issue for logical replication
- Error 1012 - Access role issue for logical replication
- Error 1014 - Database does not exist
- Error 1017 - Connection settings errors
- Error 1023 - No pg_hba.conf entry
- Error 1024 - Number of requested standby connections
- Errors Post-Pipeline Creation
-
Errors during Pipeline creation
-
PostgreSQL FAQs
- Can I track updates to existing records in PostgreSQL?
- How can I migrate a Pipeline created with one PostgreSQL Source variant to another variant?
- How can I prevent data loss when migrating or upgrading my PostgreSQL database?
- Why do FLOAT4 and FLOAT8 values in PostgreSQL show additional decimal places when loaded to BigQuery?
- Why is data not being ingested from PostgreSQL Source objects?
- Troubleshooting Database Sources
- Database Source FAQs
- File Storage
- Engineering Analytics
- Finance & Accounting Analytics
-
Marketing Analytics
- ActiveCampaign
- AdRoll
- Amazon Ads
- Apple Search Ads
- AppsFlyer
- CleverTap
- Criteo
- Drip
- Facebook Ads
- Facebook Page Insights
- Firebase Analytics
- Freshsales
- Google Ads
- Google Analytics 4
- Google Analytics 360
- Google Play Console
- Google Search Console
- HubSpot
- Instagram Business
- Klaviyo v2
- Lemlist
- LinkedIn Ads
- Mailchimp
- Mailshake
- Marketo
- Microsoft Ads
- Onfleet
- Outbrain
- Pardot
- Pinterest Ads
- Pipedrive
- Recharge
- Segment
- SendGrid Webhook
- SendGrid
- Salesforce Marketing Cloud
- Snapchat Ads
- SurveyMonkey
- Taboola
- TikTok Ads
- Twitter Ads
- Typeform
- YouTube Analytics
- Product Analytics
- Sales & Support Analytics
- Source FAQs
-
Destinations
- Familiarizing with the Destinations UI
- Cloud Storage-Based
- Databases
-
Data Warehouses
- Amazon Redshift
- Amazon Redshift Serverless
- Azure Synapse Analytics
- Databricks
- Google BigQuery
- Hevo Managed Google BigQuery
- Snowflake
- Troubleshooting Data Warehouse Destinations
-
Destination FAQs
- Can I change the primary key in my Destination table?
- Can I change the Destination table name after creating the Pipeline?
- How can I change or delete the Destination table prefix?
- Why does my Destination have deleted Source records?
- How do I filter deleted Events from the Destination?
- Does a data load regenerate deleted Hevo metadata columns?
- How do I filter out specific fields before loading data?
- Transform
- Alerts
- Account Management
- Activate
- Glossary
-
Releases- Release 2.48.1 (May 04-11, 2026)
- 2026 Releases
-
2025 Releases
- Release 2.44 (Dec 01, 2025-Jan 12, 2026)
- Release 2.43 (Nov 03-Dec 01, 2025)
- Release 2.42 (Oct 06-Nov 03, 2025)
- Release 2.41 (Sep 08-Oct 06, 2025)
- Release 2.40 (Aug 11-Sep 08, 2025)
- Release 2.39 (Jul 07-Aug 11, 2025)
- Release 2.38 (Jun 09-Jul 07, 2025)
- Release 2.37 (May 12-Jun 09, 2025)
- Release 2.36 (Apr 14-May 12, 2025)
- Release 2.35 (Mar 17-Apr 14, 2025)
- Release 2.34 (Feb 17-Mar 17, 2025)
- Release 2.33 (Jan 20-Feb 17, 2025)
-
2024 Releases
- Release 2.32 (Dec 16 2024-Jan 20, 2025)
- Release 2.31 (Nov 18-Dec 16, 2024)
- Release 2.30 (Oct 21-Nov 18, 2024)
- Release 2.29 (Sep 30-Oct 22, 2024)
- Release 2.28 (Sep 02-30, 2024)
- Release 2.27 (Aug 05-Sep 02, 2024)
- Release 2.26 (Jul 08-Aug 05, 2024)
- Release 2.25 (Jun 10-Jul 08, 2024)
- Release 2.24 (May 06-Jun 10, 2024)
- Release 2.23 (Apr 08-May 06, 2024)
- Release 2.22 (Mar 11-Apr 08, 2024)
- Release 2.21 (Feb 12-Mar 11, 2024)
- Release 2.20 (Jan 15-Feb 12, 2024)
-
2023 Releases
- Release 2.19 (Dec 04, 2023-Jan 15, 2024)
- Release Version 2.18
- Release Version 2.17
- Release Version 2.16 (with breaking changes)
- Release Version 2.15 (with breaking changes)
- Release Version 2.14
- Release Version 2.13
- Release Version 2.12
- Release Version 2.11
- Release Version 2.10
- Release Version 2.09
- Release Version 2.08
- Release Version 2.07
- Release Version 2.06
-
2022 Releases
- Release Version 2.05
- Release Version 2.04
- Release Version 2.03
- Release Version 2.02
- Release Version 2.01
- Release Version 2.00
- Release Version 1.99
- Release Version 1.98
- Release Version 1.97
- Release Version 1.96
- Release Version 1.95
- Release Version 1.93 & 1.94
- Release Version 1.92
- Release Version 1.91
- Release Version 1.90
- Release Version 1.89
- Release Version 1.88
- Release Version 1.87
- Release Version 1.86
- Release Version 1.84 & 1.85
- Release Version 1.83
- Release Version 1.82
- Release Version 1.81
- Release Version 1.80 (Jan-24-2022)
- Release Version 1.79 (Jan-03-2022)
-
2021 Releases
- Release Version 1.78 (Dec-20-2021)
- Release Version 1.77 (Dec-06-2021)
- Release Version 1.76 (Nov-22-2021)
- Release Version 1.75 (Nov-09-2021)
- Release Version 1.74 (Oct-25-2021)
- Release Version 1.73 (Oct-04-2021)
- Release Version 1.72 (Sep-20-2021)
- Release Version 1.71 (Sep-09-2021)
- Release Version 1.70 (Aug-23-2021)
- Release Version 1.69 (Aug-09-2021)
- Release Version 1.68 (Jul-26-2021)
- Release Version 1.67 (Jul-12-2021)
- Release Version 1.66 (Jun-28-2021)
- Release Version 1.65 (Jun-14-2021)
- Release Version 1.64 (Jun-01-2021)
- Release Version 1.63 (May-19-2021)
- Release Version 1.62 (May-05-2021)
- Release Version 1.61 (Apr-20-2021)
- Release Version 1.60 (Apr-06-2021)
- Release Version 1.59 (Mar-23-2021)
- Release Version 1.58 (Mar-09-2021)
- Release Version 1.57 (Feb-22-2021)
- Release Version 1.56 (Feb-09-2021)
- Release Version 1.55 (Jan-25-2021)
- Release Version 1.54 (Jan-12-2021)
-
2020 Releases
- Release Version 1.53 (Dec-22-2020)
- Release Version 1.52 (Dec-03-2020)
- Release Version 1.51 (Nov-10-2020)
- Release Version 1.50 (Oct-19-2020)
- Release Version 1.49 (Sep-28-2020)
- Release Version 1.48 (Sep-01-2020)
- Release Version 1.47 (Aug-06-2020)
- Release Version 1.46 (Jul-21-2020)
- Release Version 1.45 (Jul-02-2020)
- Release Version 1.44 (Jun-11-2020)
- Release Version 1.43 (May-15-2020)
- Release Version 1.42 (Apr-30-2020)
- Release Version 1.41 (Apr-2020)
- Release Version 1.40 (Mar-2020)
- Release Version 1.39 (Feb-2020)
- Release Version 1.38 (Jan-2020)
- Early Access New
On This Page
Amazon RDS for Oracle is a fully managed commercial database that makes it easy to set up, operate, and scale Oracle deployments in the cloud. Amazon RDS frees you up to focus on innovation and application development by managing time-consuming database administration tasks including provisioning, backups, software patching, monitoring, and hardware scaling.
Refer to Oracle on Amazon RDS for the supported Oracle database versions.
Prerequisites
-
Oracle database version is 12c or above.
-
Redo Log replication is enabled, if ingestion mode is RedoLog.
Note: Hevo supports Redo Log ingestion mode for Oracle database 19c and higher in Pipelines created after Release 1.96.
-
Hevo’s IP addresses are whitelisted. The database user must have
CREATE/MANAGE SECURITY GROUPSprivileges in Amazon RDS to do this. -
Database hostname and port number of the Source instance are available.
-
You are assigned the Team Administrator, Team Collaborator, or Pipeline Administrator role in Hevo, to create the Pipeline.
Perform the following steps to configure your Amazon RDS Oracle Source:
Set up Redo Logs for Replication
A redo log is a collection of log files that record information about modifications made to data objects on an Oracle server instance. Oracle LogMiner uses redo logs to track these modifications and determine the rows requiring updates in the Destination system.
To set up redo logs for replication, connect to your Oracle server and perform the following steps:
1. Enable ARCHIVE Log
You need to enable archiving for redo logs.
To do this:
-
Check the current log mode. This should be
ARCHIVELOG.SELECT LOG_MODE FROM "V$DATABASE"; -
Enable
ARCHIVELOGmode if the current log mode isNOARCHIVELOG.BEGIN rdsadmin.rdsadmin_util.set_configuration('archivelog retention hours', 72); END;Note: The minimum value for
archivelog retention hoursis 72. The archive log retention must be 72 hours at a minimum. This avoids any data loss that may occur due to downtimes in the Source database.
2. Enable supplemental logging
Supplemental logging ensures that the Oracle server logs all the columns of every changed Event.
-
Check if supplemental logging is enabled:
SELECT SUPPLEMENTAL_LOG_DATA_MIN FROM "V$DATABASE";This returns either of the following values:
-
YES: Represents that the supplemental logging is enabled. -
IMPLICIT: Represents that the supplemental logging is disabled.
-
-
If the value returned in the previous step is
IMPLICIT, enable supplemental logging of primary key columns :BEGIN rdsadmin.rdsadmin_util.alter_supplemental_logging('ADD','ALL'); END; -
Optionally, if you’re using Oracle 12, grant the following permission:
GRANT LOGMINING TO "<user_name>";
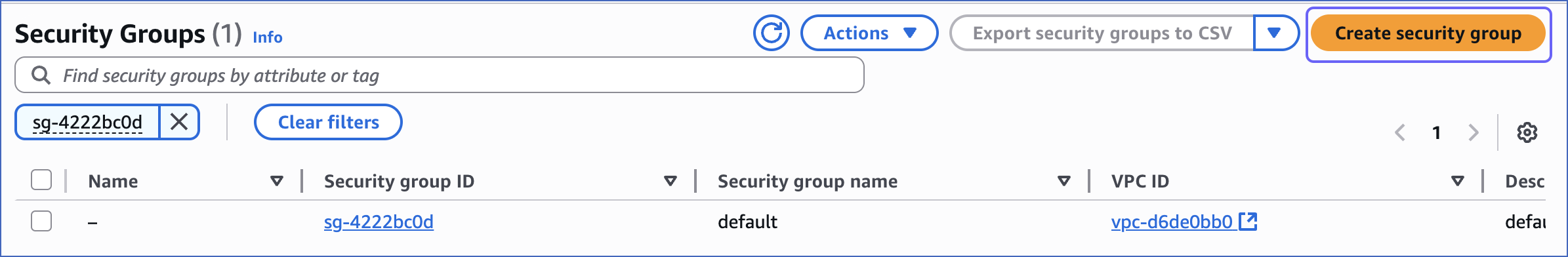
Whitelist Hevo’s IP Addresses
You need to whitelist the Hevo IP address for your region to enable Hevo to connect to your Amazon RDS Oracle database. You can do this by creating a VPC security group and adding inbound and outbound access rules for the Hevo IP addresses. A VPC group controls access to the database instances and virtual server instances inside a VPC. To do this:
1. Create a VPC security group
-
Access the Amazon RDS console.
-
In the left navigation pane, under Dashboard, select Databases (or Instances if you are using an older version).
-
In the Databases section on the right, select the read replica or master database instance that you want to connect.

-
In the Connectivity & security tab, click the hyperlink under Security, VPC security groups.

-
On the Security Groups page, click Create security group.
You can also select an existing group, which you have used for other database instances, and modify it.
-
On the Create security group page, specify the following:
-
Security group name: An appropriate name for the security group.
-
Description: A brief description of the security group.
-
VPC ID: A unique identifier for the VPC.
-
2. Add inbound rules
In the Inbound Rules section:
-
Click Add rule and specify the following:

-
Port range: The port of your Amazon RDS Oracle instance. For example, 1521.
-
Source: Select Custom from the drop-down and enter Hevo’s IP addresses for your region.
-
-
Add more rules for all the Hevo IPs you want to whitelist.
-
Click Create security group.
Create a Database User and Grant Privileges
You can log in to Oracle as a masteruser or create a new database user for Hevo.
1. Create a database user (optional)
If a database user does not exist already, create a database user by logging in to Oracle as a masteruser and entering the following commands:
CREATE USER "hevo" IDENTIFIED BY "password";
GRANT CONNECT, CREATE SESSION TO "hevo";
2. Grant privileges to the user
The database user you specify in the Hevo Pipeline must have the SELECT privilege.
To assign this privilege, log in to Oracle as a masteruser or a user with GRANT privilege and enter the following commands:
-
Grant SELECT privilege to all or specific tables:
-- Grant access to all tables GRANT SELECT ANY TABLE TO "hevo"; -- Grant access to specific tables GRANT SELECT ON "<schema>"."<table>" TO "hevo"; -
Optionally, if you are using Redo Logs as the Pipeline mode, grant access to Oracle LogMiner:
GRANT SELECT ON SYS.V_$DATABASE TO "hevo"; GRANT SELECT ON SYS.V_$ARCHIVED_LOG TO "hevo"; GRANT SELECT ON SYS.V_$LOGMNR_CONTENTS TO "hevo"; GRANT EXECUTE ON DBMS_LOGMNR TO "hevo"; GRANT EXECUTE ON DBMS_LOGMNR_D TO "hevo";
Now you can try connecting to Oracle using Redo Logs pipeline mode, with the user configured in the above steps.
Retrieve the Hostname, Service ID, and Port Number
Note: The RDS hostnames start with your database name and end with rds.amazonaws.com.
For example:
Host: oracle-database-1.xxxxxxxxx.rds.amazonaws.com
Service ID: ORCL
Port: 1521
-
In the left navigation pane of the Amazon RDS console, click Databases (or Instances if you are using an older version).
-
In the Databases section on the right, click the DB identifier of the Amazon RDS Oracle instance.

-
Click the Connectivity & security tab, and copy the values under Endpoint and Port as the hostname and port number. You will specify these while creating your Hevo Pipeline.
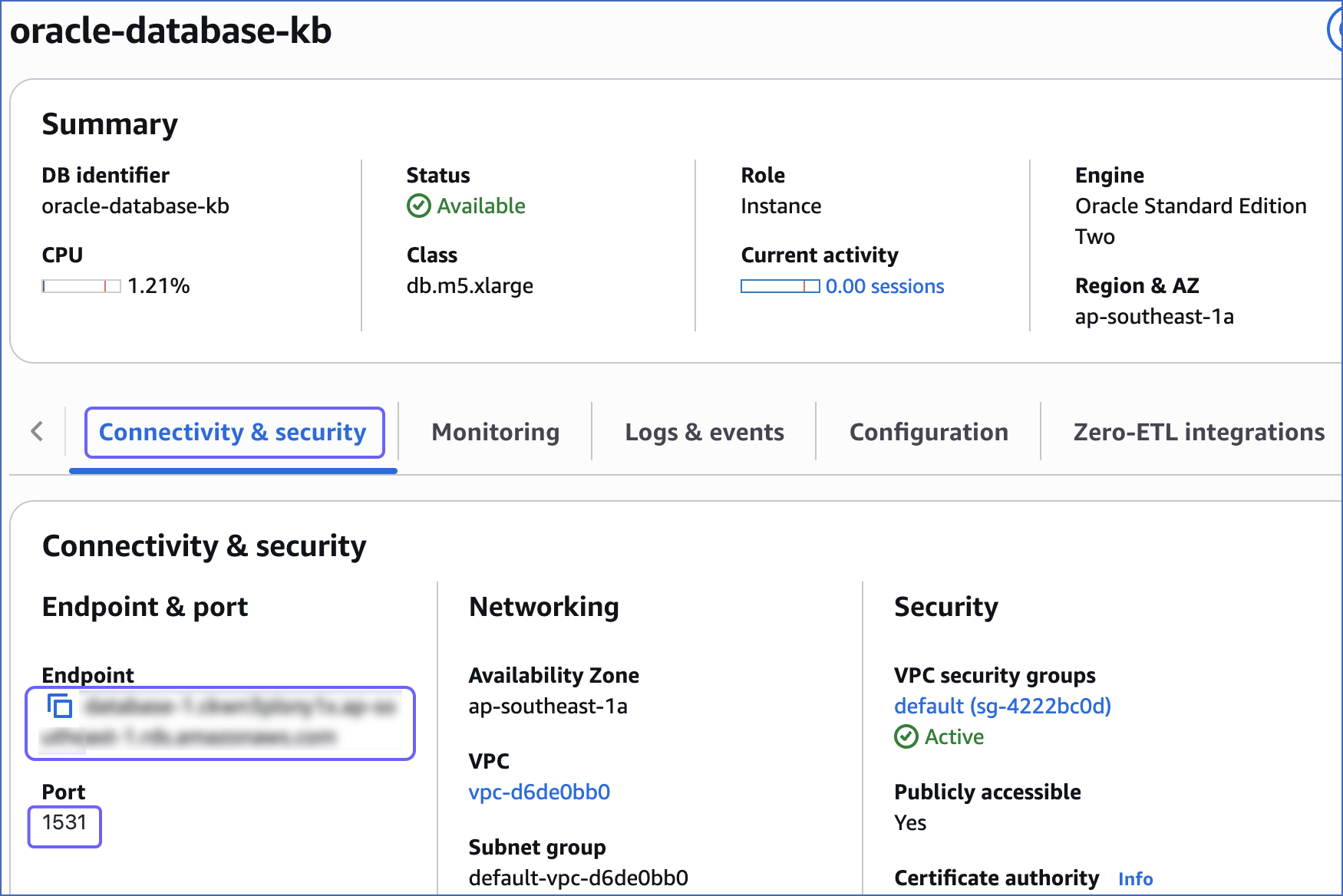
-
Click the Configuration tab, and copy the value under DB name. You will use this DB name as the Service Name while creating your Pipeline.

Specify Amazon RDS Oracle Connection Settings
Perform the following steps to configure Amazon RDS Oracle as a Source in Hevo:
-
Click PIPELINES in the Navigation Bar.
-
Click + Create Pipeline in the Pipelines List View.
-
On the Select Source Type page, select Amazon RDS Oracle.
-
On the Select Destination Type page, select the type of Destination you want to use.
-
On the page that appears, do the following:
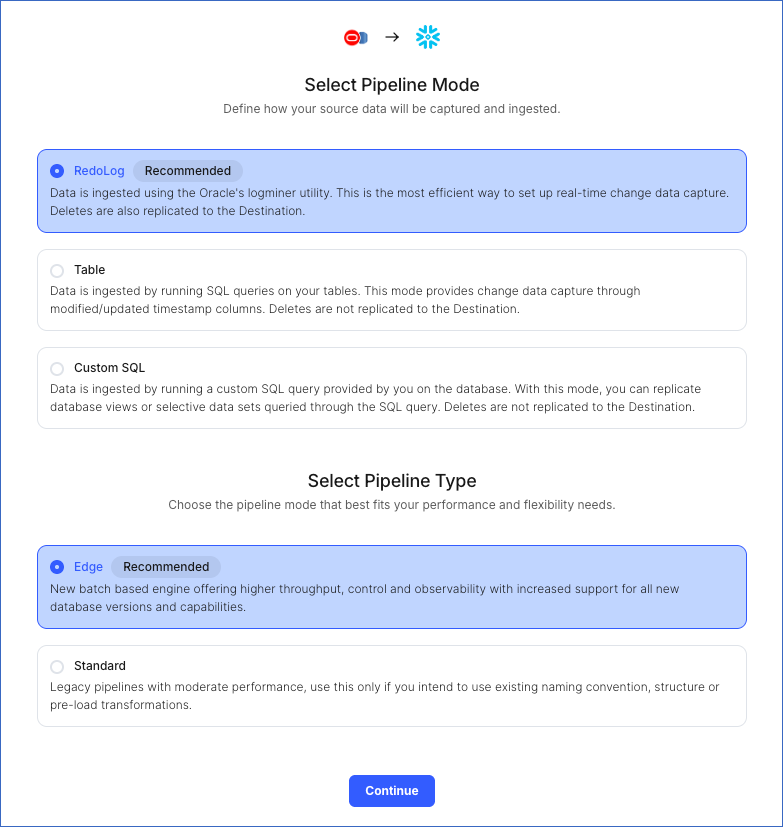
-
Select Pipeline Mode: Choose the mode for ingesting data from the Source. Default value: RedoLog. The available modes are RedoLog, Table, and Custom SQL.
Depending on the Pipeline mode you select, you must configure the objects to be replicated. Refer to section, Object and Query Mode Settings for the steps to do this.
Note: For Custom SQL Pipeline mode, all Events loaded to the Destination are billable.
-
Select Pipeline Type: Choose the type of Pipeline you want to create based on your requirements, and then click Continue.
-
If you select Edge, read Amazon RDS Oracle to configure your Edge Pipeline.
-
If you select Standard, skip to step 6 below.
This section is displayed only if all the following conditions are met:
-
The selected Destination type is supported in Edge.
-
The Pipeline mode is set to RedoLog.
-
Your Team was created before September 15, 2025, and has an existing Pipeline created with the same Destination type and Pipeline mode.
For Teams that do not meet the above criteria, if the selected Destination type is supported in Edge and the Pipeline mode is set to RedoLog, you can proceed to create an Edge Pipeline. Read Amazon RDS Oracle to configure your Edge Pipeline. Otherwise, you can proceed to create a Standard Pipeline.
-
-
-
On the Configure your Amazon RDS Oracle Source page, specify the following:
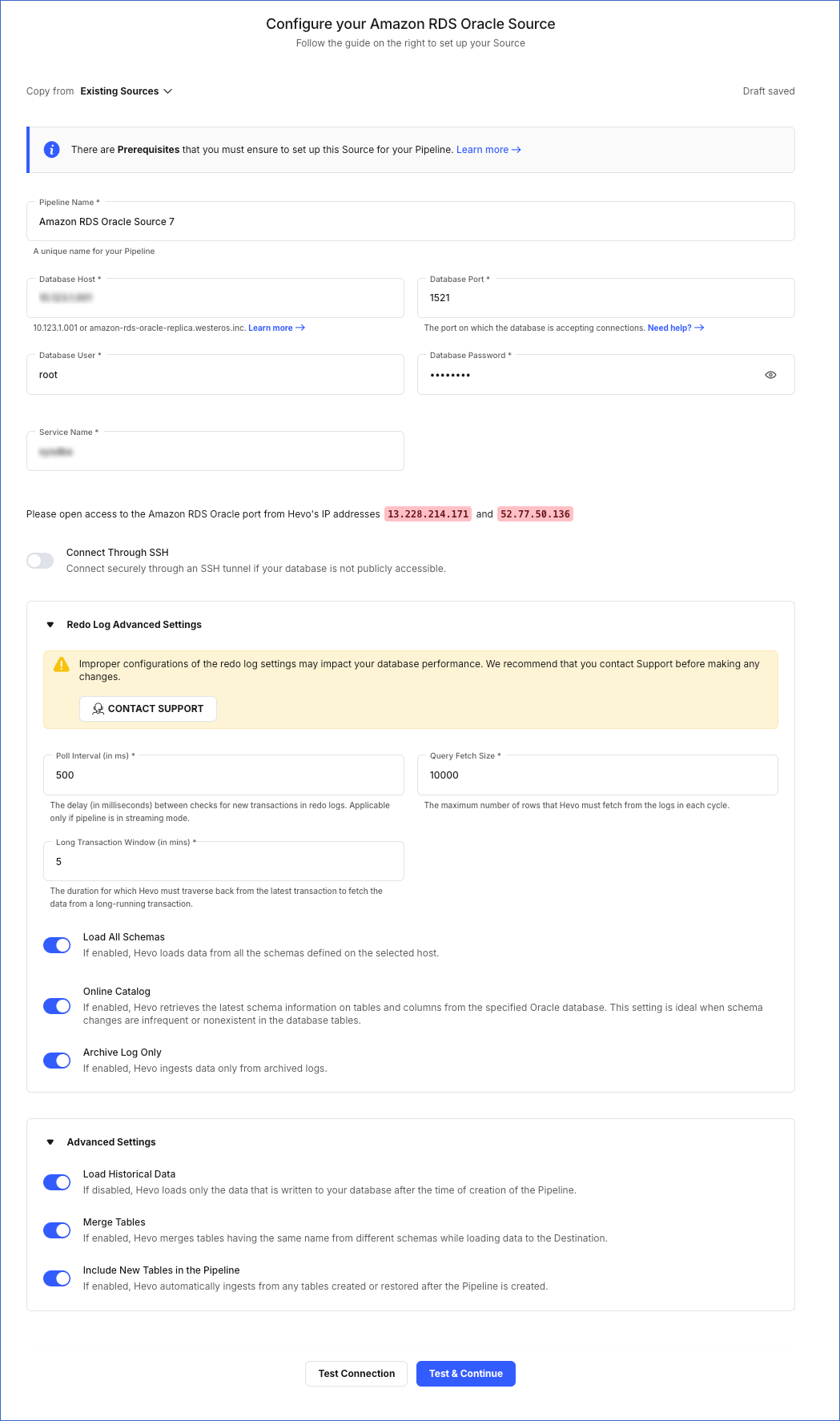
-
Pipeline Name: A unique name for your Pipeline, not exceeding 255 characters.
-
Database Host: The Oracle database host’s IP address or DNS.
The following table lists a few examples of Oracle hosts:
Variant Host Amazon RDS Oracle oracle-rds-1.xxxxx.rds.amazonaws.com Generic Oracle 192.168.2.5 Note: For URL-based hostnames, exclude the http:// or https:// part. For example, if the hostname URL is https://oracle-rds-1.xxxxx.rds.amazonaws.com, enter oracle-rds-1.xxxxx.rds.amazonaws.com.
-
Database Port: The port on which your Amazon RDS Oracle server listens for connections. Default value: 1521.
-
Database User: The authenticated user who has the permissions to read tables in your database.
-
Database Password: The password for the database user.
-
Redo Log Advanced Settings: This section is applicable if RedoLog is selected as an ingestion mode:
Note: Any modification in the default value of the following settings may impact your database performance. We recommend that you contact Hevo Support before making any changes.
-
Poll Interval (in ms): The delay in milliseconds between the checks that Hevo makes to search for new transactions in the redo logs. Default value: 500.
-
Query Fetch Size: The maximum number of rows that Hevo fetches from the logs in each query. Default value: 10,000.
-
Long Transaction Window (in mins): The duration in minutes that Hevo must traverse back from the current transaction to fetch the data in a long-running transaction. Default value: 5.
Note: Increasing the default value can lead to increased memory consumption by the Source database during log mining sessions.
-
Load All Schemas: If enabled, Hevo loads data for all the schemas.
If disabled, Hevo loads data from the schema(s) that you specify in a comma-separated list.
-
Online Catalog: If enabled, Hevo retrieves the updated schema information from the specified Oracle database. This setting is ideal when schema changes are infrequent or nonexistent in the database tables.
If disabled, Hevo retrieves the schema information from the copy that Hevo maintains.
Note: This option is non-editable post-Pipeline creation.
-
Archive Log Only: If enabled, Hevo ingests data only from the archived redo logs.
If disabled, Hevo ingests data from the archived and online redo logs.
-
-
Connect through SSH: Enable this option to connect to Hevo using an SSH tunnel, instead of directly connecting your Oracle database host to Hevo. This provides an additional level of security to your database by not exposing your Oracle setup to the public. Read Connecting Through SSH. To set up an SSH tunnel for your Amazon RDS Oracle database hosted on Amazon Web Services (AWS), read Configuring an SSH Tunnel.
If this option is disabled, you must whitelist Hevo’s IP addresses to allow Hevo to connect to your Oracle database host. Refer to the content for your Oracle variant for steps to do this.
-
Advanced Settings:
-
Load Historical Data: Applicable for Pipelines created with RedoLog or Table mode. If this option is enabled, the entire table data is fetched during the first run of the Pipeline. If disabled, Hevo loads only the records written to your database after the Pipeline was created.
-
Merge Tables: If enabled, Hevo merges tables with the same name from different databases while loading the data to the warehouse. Hevo loads the Database Name field with each record.
If disabled, Hevo adds the database name as prefix to each table name. Read How does the Merge Tables feature work?.
This option is applicable only for Pipelines with RedoLog mode.
-
Include New Tables in the Pipeline: Applicable for all ingestion modes except Custom SQL.
If enabled, Hevo automatically ingests data from tables created in the Source after the Pipeline has been built. These may include completely new tables or previously deleted tables that have been re-created in the Source. All data for these tables is ingested using database logs, making it incremental.
If disabled, new and re-created tables are not ingested automatically. They are added in SKIPPED state in the objects list, on the Pipeline Overview page. You can update their status to INCLUDED to ingest data.
You can change this setting later.
-
-
-
Click Test Connection. This button is enabled once you specify all the mandatory fields. Hevo’s underlying connectivity checker validates the connection settings you provide.
-
Click Test & Continue to proceed for setting up the Destination. This button is enabled once you specify all the mandatory fields.
Object and Query Mode Settings
Once you have specified the Source connection settings in Step 5 above, do one of the following:
-
For Pipelines configured with the Table or RedoLog mode:
-
On the Select Objects page, select the objects you want to replicate and click Continue.

Note:
-
Each object represents a table in your database.
-
From Release 2.19 onwards, for log-based Pipelines, you can keep the objects listed on the Select Objects page deselected by default. In this case, when you skip object selection, all objects are skipped for ingestion, and the Pipeline is created in the Active state. You can include the required objects post-Pipeline creation. Contact Hevo Support to enable this option for your teams.
-
-
On the Configure Objects page, specify the query mode you want to use for each selected object.

-
-
For Pipelines configured with the Custom SQL mode:
-
On the Provide Query Settings page, enter the custom SQL query to fetch data from the Source.
-
In the Query Mode drop-down, select the query mode, and click Continue.

-
Data Replication
| For Teams Created | Ingestion Mode | Default Ingestion Frequency | Minimum Ingestion Frequency | Maximum Ingestion Frequency | Custom Frequency Range (in Hrs) |
|---|---|---|---|---|---|
| Before Release 2.21 | Table | 15 Mins | 5 Mins | 24 Hrs | 1-24 |
| Log-based | 5 Mins | 5 Mins | 1 Hr | NA | |
| After Release 2.21 | Table | 6 Hrs | 30 Mins | 24 Hrs | 1-24 |
| Log-based | 30 Mins | 30 Mins | 12 Hrs | 1-24 |
Note: The custom frequency must be set in hours as an integer value. For example, 1, 2, or 3 but not 1.5 or 1.75.
-
Historical Data: In the first run of the Pipeline, Hevo ingests all available data for the selected objects from your Source database.
-
Incremental Data: Once the historical load is complete, data is ingested as per the ingestion frequency.
Additional Information
Read the detailed Hevo documentation for the following related topics:
Limitations
-
Hevo does not support the flashback method to track incremental updates.
-
Redo Log does not support user-defined data types. Therefore, fields with such data types are not captured in the log and are lost.
-
Hevo does not load data from a column into the Destination table if its size exceeds 16 MB, and skips the Event if it exceeds 40 MB. If the Event contains a column larger than 16 MB, Hevo attempts to load the Event after dropping that column’s data. However, if the Event size still exceeds 40 MB, then the Event is also dropped. As a result, you may see discrepancies between your Source and Destination data. To avoid such a scenario, ensure that each Event contains less than 40 MB of data.
See Also
Revision History
Refer to the following table for the list of key updates made to this page:
| Date | Release | Description of Change |
|---|---|---|
| Nov-12-2025 | NA | Updated the document as per the latest Hevo UI. |
| Oct-27-2025 | NA | Updated sections, Retrieve the Hostname, Service ID, and Port Number and Whitelist Hevo’s IP Address as per the latest Amazon RDS UI. |
| Oct-13-2025 | NA | Updated section, Specify Amazon RDS Oracle Connection Settings to clarify when the Select Pipeline Type section is displayed during Pipeline configuration. |
| Oct-09-2025 | NA | Updated section, Specify Amazon RDS Oracle Connection Settings to mention that the Load Historical Data option is also applicable for Pipelines created with Table mode. |
| Sep-18-2025 | NA | Updated section, Specify Amazon RDS Oracle Connection Settings as per the latest UI. |
| Aug-1-2025 | NA | Added clarification that data ingested from new and re-created tables is billable. |
| Jul-07-2025 | NA | Updated the Limitations section to inform about the max record and column size in an Event. |
| Jan-07-2025 | NA | Updated the Limitations section to add information on Event size. |
| Nov-18-2024 | NA | Updated section, Specify Amazon RDS Oracle Connection Settings as per the latest Hevo UI. |
| Apr-29-2024 | NA | Updated section, Specify Amazon RDS Oracle Connection Settings to include more detailed steps. |
| Mar-05-2024 | 2.21 | Added the Data Replication section. |
| Jan-22-2024 | 2.19.2 | Updated section, Object and Query Mode Settings to add a note about the enhanced object selection flow available for log-based Pipelines. |
| Jan-10-2024 | 2.19 | Updated section, Specify Amazon RDS Oracle Connection Settings as per latest Hevo functionality. |
| Nov-03-2023 | NA | Added section, Object and Query Mode Settings. |
| Apr-21-2023 | NA | Updated section, Specify Amazon RDS Oracle Connection Settings to add a note to inform users that all loaded Events are billable for Custom SQL mode-based Pipelines. |
| Mar-09-2023 | 2.09 | Updated section, Specify Amazon RDS Oracle Connection Settings to mention about SEE MORE in the Select an Ingestion Mode section. |
| Dec-19-2022 | 2.04 | Updated section, Specify Amazon RDS Oracle Connection Settings to add information that you must specify all fields to create a Pipeline. |
| Dec-07-2022 | 2.03 | Updated section, Specify Oracle Connection Settings to mention about including skipped objects post-Pipeline creation. |
| Dec-07-2022 | 2.03 | Updated section, Specify Oracle Connection Settings to mention about the connectivity checker. |
| Feb-07-2022 | 1.81 | Updated section, Whitelist Hevo’s IP Address to remove details about Outbound rules as they are not required. |
| Dec-06-2021 | 1.77 | Added a See Also link to the Pipeline failure due to Redo Log expiry page. |
| Nov-22-2021 | NA | Updated the Limitations section. |
| Mar-09-2021 | 1.58 | Added section Retrieve the Hostname, Service ID, and Port Number. |